The Red And Blue Leak That's Breaking The Internet!
What happens when political scandals, data breaches, and social media controversies collide in the digital age? The answer is the "Red and Blue Leak" that has taken the internet by storm, creating chaos across multiple platforms and industries. This unprecedented series of events has captivated millions worldwide, raising serious questions about privacy, security, and the power of information in our interconnected world.
The saga began with what appeared to be a routine political deposition but quickly spiraled into a complex web of leaked information, social media frenzy, and international implications. From congressional offices to fashion runways, no sector has remained untouched by this digital tsunami. As we dive deeper into this phenomenon, we'll uncover how seemingly unrelated events have converged to create one of the most significant information breaches in recent history.
The Political Spark: Lauren Boebert and the Clinton-Epstein Connection
The controversy ignited when Lauren Boebert's photo leak became intertwined with the Hillary Clinton-Epstein deposition proceedings. Influencer Benny Johnson claimed the photo originated from Representative Boebert's office, setting off a chain reaction that would soon engulf the political landscape.
- Leaked The 5 Second Short Hair Trick Thats Breaking The Internet
- Coral Island Silver Arowana Leak What Theyre Hiding From You Will Shock You
This incident highlights the increasingly blurred lines between political figures, social media influencers, and information dissemination. The rapid spread of the image across platforms demonstrated how quickly political content can morph into viral sensations, often losing context and accuracy in the process. Political analysts have noted that this event marks a new era in how congressional activities are documented and shared with the public.
The deposition itself, already a matter of significant public interest, became further complicated by the photo leak. Questions arose about the security protocols in place for sensitive political proceedings and the role of social media in shaping public perception of governmental processes. The incident has sparked debates about transparency versus privacy in political operations and the responsibilities of elected officials in the digital age.
The Skylar Blue Data Breach: A Digital Catastrophe
As political tensions simmered, the Skylar Blue leak erupted onto the scene, representing one of the most significant data breaches in recent memory. This massive security failure impacted millions of users across various online platforms, exposing sensitive personal information and creating a crisis of digital trust.
- Leaked Videos Reveal How Big Booty White Girls Are Dominating The Internet
- How To Use Batana Oil For Hair Growth The Leaked Guide Everyones Talking About
The breach's scope was unprecedented, affecting everything from social media accounts to financial records. Cybersecurity experts estimate that the compromised data could take years to fully contain and mitigate. The incident has prompted a widespread reevaluation of data protection practices among major tech companies and has led to calls for stricter regulatory oversight of digital security measures.
Users affected by the Skylar Blue leak have reported various consequences, from identity theft attempts to targeted phishing scams. The breach has also raised questions about the responsibility of platforms in protecting user data and the adequacy of current cybersecurity measures in an increasingly connected world.
Social Media's Role: YouTube, Google Trends, and Viral Content
In the wake of these scandals, social media platforms have become both the battleground and the amplifier for the unfolding drama. YouTube, as one of the largest content-sharing platforms, has seen a surge in videos analyzing and discussing the various leaks. Content creators have capitalized on the public's thirst for information, producing everything from investigative reports to conspiracy theory videos.
Google Trends has provided a fascinating window into public interest, with search terms related to the leaks dominating the platform. The geographic distribution of searches has revealed interesting patterns, with certain regions showing disproportionate interest in specific aspects of the controversy. This data has proven invaluable for understanding the global impact of the leaks and the varying concerns of different populations.
The phenomenon has also highlighted the power of social media algorithms in shaping public discourse. As users engage with content related to the leaks, platforms' recommendation systems create feedback loops that can amplify certain narratives while suppressing others. This has led to concerns about echo chambers and the potential for misinformation to spread unchecked in the digital ecosystem.
The Fashion Industry Fallout: Bonnie Blue Scandal
Perhaps one of the most unexpected casualties of the digital chaos has been the fashion industry, rocked by the Bonnie Blue leaks. This scandal, which initially seemed unrelated to the political and data breaches, has proven to be a significant chapter in the ongoing saga.
The leaks exposed internal communications and design documents from major fashion houses, revealing everything from upcoming collections to controversial business practices. The impact on the industry has been profound, with stock prices of affected companies fluctuating wildly and consumer trust in luxury brands taking a significant hit.
The Bonnie Blue incident has also sparked discussions about intellectual property rights in the digital age and the vulnerability of creative industries to cyber attacks. Fashion insiders have noted that the leaks have accelerated trends towards digitalization in the industry, with many brands rushing to implement stronger cybersecurity measures and rethinking their approach to online presence.
Cybersecurity Crisis: NSA Malware and Global Hijacking
As the various leaks continued to dominate headlines, a new threat emerged in the form of leaked NSA malware. This sophisticated software, originally developed for national security purposes, found its way into the hands of malicious actors who began using it to hijack computers around the world.
The scale of this cybersecurity crisis is staggering, with experts estimating that millions of devices have been compromised. The malware's capabilities allow for everything from data theft to complete system control, posing a significant threat to both individual users and large organizations. Governments worldwide have issued warnings and are working to develop countermeasures, but the decentralized nature of the threat makes it particularly challenging to contain.
This development has reignited debates about government surveillance, the ethics of developing powerful cyber weapons, and the risks of such tools falling into the wrong hands. It has also highlighted the interconnected nature of global cybersecurity, with vulnerabilities in one nation's systems potentially affecting users worldwide.
Media Coverage and Public Response
The complexity and scale of the "Red and Blue Leak" have challenged traditional media outlets to adapt their coverage strategies. Major publications like The Atlantic and Reuters have provided in-depth analysis and breaking news updates, while cable news networks have dedicated significant airtime to the unfolding events.
The public response has been equally multifaceted. Online forums and social media platforms have become hubs for discussion, speculation, and sometimes misinformation. Fact-checking organizations have worked overtime to combat false narratives, but the sheer volume of information has made this a daunting task.
Political figures have found themselves under increased scrutiny, with every statement and action analyzed for potential connections to the leaks. This heightened attention has led to a more engaged but also more polarized public discourse, with different segments of the population interpreting events through vastly different lenses.
The Chicago Connection: Local Impact and National Implications
While much of the focus has been on national and international implications, the leaks have also had a significant impact on local communities. In Chicago, for instance, the Chicago Tribune has reported extensively on how the various scandals have affected local businesses, political figures, and residents.
The city's diverse population has led to a wide range of responses to the leaks, with different communities focusing on aspects most relevant to their interests and concerns. This local perspective has provided valuable insights into how global digital phenomena can have very real and immediate impacts on individual lives and communities.
Chicago's experience also highlights the role of local journalism in providing context and analysis that national outlets might miss. The city's reporters have uncovered connections between the leaks and local political machinations, business dealings, and social movements, demonstrating the far-reaching tentacles of this digital crisis.
Technology and the Future: Lessons Learned
As the dust begins to settle on the initial wave of leaks, attention is turning to the future of digital security and information management. Tech experts and policymakers are grappling with the challenge of preventing similar incidents while preserving the benefits of an open and connected digital ecosystem.
The concept of "digital resilience" has emerged as a key theme in discussions about moving forward. This approach emphasizes not just preventing breaches but also developing robust systems for rapid response and recovery when incidents do occur. It also involves educating users about digital literacy and the importance of personal cybersecurity practices.
The leaks have also accelerated discussions about the role of artificial intelligence in both causing and preventing digital crises. While AI systems were used to analyze and spread information about the leaks, they are also being developed as tools for detecting and mitigating security threats in real-time.
Conclusion: Navigating the New Digital Landscape
The "Red and Blue Leak" saga represents a watershed moment in our digital history. It has exposed the vulnerabilities of our interconnected world while also showcasing the power of information in shaping public discourse and driving social change. As we move forward, the lessons learned from this crisis will be crucial in building a more secure and resilient digital future.
The events have underscored the need for a multi-faceted approach to digital security, involving not just technological solutions but also policy reforms, educational initiatives, and a rethinking of our relationship with information in the digital age. They have also highlighted the importance of critical thinking and media literacy in navigating an increasingly complex information landscape.
As individuals, organizations, and societies, we must adapt to this new reality where the boundaries between the physical and digital worlds are increasingly blurred. The "Red and Blue Leak" may have been a crisis, but it also presents an opportunity to reimagine and rebuild our digital infrastructure for a more secure and equitable future.
- Fixer Upper Divorce
- The Beastmans Secret Heat Cycle What They Dont Want You To Know About The Nude Scandal

Leak Red - Kei Jhnea | Album | AllMusic
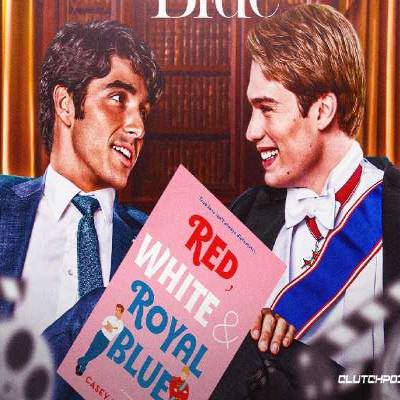
Red-White-Royal-Blue-review | Downpit
Behind Blue Eyes: BREAKING THE INTERNET... Well, maybe not yet.